January Supplemental
March 2017 Notes
February 2017 Notes
February 15, 2017
tensmiths
Uncategorized
February FTF will commence at 1400 on the 26th in our park location. Items to discuss will mostly detail how to carry out the training schedule for the spring/summer. Bring your notebooks.
Sun Tsu was an early strategist on warfare and put his ideas into print around 500 BC. His book guides both strategists and practitioners of warfare even today.
1500 years later, events in feudal Japan lead to the rise of the Samurai. During a civil war, the Minamoto and Taira samurai clans rose to prominence. They fought one another in the Heiji Rebellion (1160). After their victory, the Taira established the first samurai-led government. The defeated Minamoto were banished from the capital at Kyoto.

Another 500 years later, The Book of Five Rings, a text on kenjutsu and the martial arts in general, was written by the swordsman Miyamoto Musashi (1645).

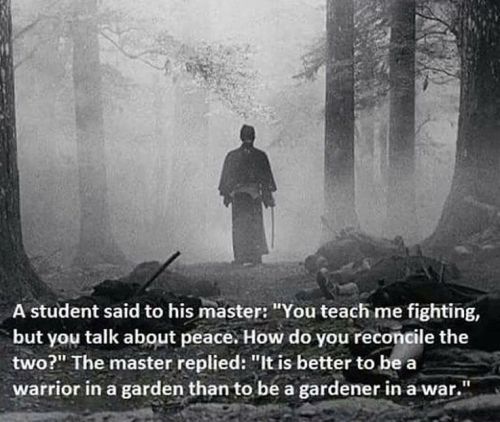
Two thousand years sounds like a long time for the distillation of what seems such a simple concept, doesn’t it?
Locally, the mind-set of Sun Tsu and Musashi are put into real-life practice in our Robin Sage FTX, already on the calendar. Details of the big “Who, Why, How, When, and Where” describes the extent of the exercise in the SFODA learning curve. Last year’s preview:
“The exercise’s notional country of Pineland encompasses Alamance, Anson, Cabarrus, Chatham, Davidson, Guilford, Hoke, Montgomery, Moore, Randolph, Richmond, Rowan, Scotland, Stanly and Union counties. Throughout the exercise, Special Forces candidates and Robin Sage role-players not only conduct training missions such as controlled assaults and key-leader engagements, but also live, eat and sleep in these civilian areas.”
And a year has passed since last spring, when the DHS and FBI released an intelligence assessment on the Baseline Comparison of US and Foreign Anarchist Extremist Movements.

“(U//FOUO) The vast majority of US anarchist extremist attacks targeted property likely due to the location’s accessibility and as a symbol of capitalism and globalization. Most foreign anarchist extremist attacks targeted persons likely because of the cohesiveness of the movement and greater emphasis on issues that can be blamed on local, individual targets. US anarchist extremists targeted the banking/finance sector most often, as these perceived soft targets of capitalism are possible to attack with tactics that are non-lethal yet cause significant economic damage and pose significant public safety risks. Foreign anarchist extremists most often targeted government entities, likely due to the emphasis placed on local domestic issues by foreign anarchist extremists and their capabilities to commit attacks against hardened targets.”
How many attacks by extremist have taken place, domestically and over seas since then, and have they followed the same pattern? The real question being, “Is there an identifiable rise in domestic violence and acts of terrorism? And is there a common source of funding and organizational support for those groups involved?”
Maybe the most telling graph –

Our scenario planning model that we’ve used for the past several years needs a little updating in light of events since November 2016. As much as the SPLC makes its money exploiting information of dubious value concerning Militias and White Supremacists groups (they equate the prevalence of both to the same factors), there is so far no equivalent place to discover all the various groups (largely funded by the same organizations) that are trying to emerge as major players in the general effort to cause disruptions for the edification of the Main Stream Media. Here are but a few, but you might get the feeling they aren’t lacking for motivation and convictions, much like any other terrorist group. And a few others that might be a source of training to counter those groups. Keep in mind that there are still elements in the government that are enabling these groups despite having the responsibility to protect the public from these groups.
“You may think that, boisterous as these demonstrators are, and although they can draw a few thousand youngsters to their events, they are but a tiny fraction of the population and could never pose a serious threat to any government. But how wrong you would be.”
Paul Sperry wrote earlier this week in the New York Post how former president Obama is actively sabotaging President Trump.
“He’s doing it through a network of leftist nonprofits led by Organizing for Action. Normally you’d expect an organization set up to support a politician and his agenda to close up shop after that candidate leaves office, but not Obama’s OFA. Rather, it’s gearing up for battle, with a growing war chest and more than 250 offices across the country.
Since Donald Trump’s election, this little-known but well-funded protesting arm has beefed up staff and ramped up recruitment of young liberal activists, declaring on its website, “We’re not backing down.” Determined to salvage Obama’s legacy, it’s drawing battle lines on immigration, ObamaCare, race relations and climate change.”
“We’re Agency, an anarchist media relations project since 2013. During Occupy anarchist ideas also enjoyed greater coverage, but we noticed that most stories focused on the same few anarchist voices over and over. As anarchism is garnering more and more interest now, we want to broaden the voices and ideas that show up in the news.”
Learn how to execute Red Team Operations properly by converging Penetration Testing, Social Engineering and Physical Security tactics.
What you will learn –
Full-cycle Red Teaming from Operational Planning to Reporting phase
How to converge technical, personnel and physical vulnerabilities
Covert and overt methods of entry into a target location
Social engineering tactics, from telephone to face-to-face (see our book)
Evasion, lock picking and other bypass techniques
Physical security scouting and reconnaissance
Penetration testing for Red Team Operations
What you will do –
Full-training Exercises (FTX)
Plan, execute and report on a full-training Red Team Operation
Conduct target reconnaissance both offline and online
Clone RFID badges, steal/impress keys, pick locks or bypass security controls
Exploit system vulnerabilities on the target’s network
Use several social engineering tactics to gather information from targets
Make overt and covert entry into a target location and establish APT persistence

From the old REDTEAMS Website:
“Most people are starting to realize that there are only two different types of companies in the world: those that have been breached and know it and those that have been breached and don’t know it.”
Rule 1: Always have an escape plan
Rule 2: Never get caught.
Rule 3: Be aware of your surroundings.
Rule 4: Always have a backup plan.
Rule 5: Assumption is the mother of all fuckups.
Rule 6: Trust your gut.
Rule 7: Simple and light equals freedom, agility and mobility.
Rule 8: KISS: Keep it simple, stupid.
Rule 9: The solution is in the problem.
Rule 10: Don’t become predictable.
Rule 11: Never take the elevator.
Rule 12: Act, don’t react.

View at Medium.com
The more you hack in peace, the less you bleed in war
“Hacking takes time. Developing the tool chain takes time, recon takes time, sometimes systems get hardened and the optimal time to hack them was in the past, and so on and so on. The best time to collect intelligence about an adversary is before you need it.”
The road ahead promises to be full of challenges for the next few years.
January Supplemental
March 2017 Notes







 Arizona Border Recon
Arizona Border Recon Militia Friends
Militia Friends Order of the Arrow — B. S. A.
Order of the Arrow — B. S. A. Trail Life USA
Trail Life USA American Defense Manufacturing
American Defense Manufacturing First Spear
First Spear Going Gear
Going Gear Grey Ghost Gear
Grey Ghost Gear Hill People Gear
Hill People Gear Last Ditch Kit
Last Ditch Kit London Bridge Trading
London Bridge Trading Mil-Spec Monkey
Mil-Spec Monkey Old Grouch's Military Surplus
Old Grouch's Military Surplus Outdoor Limited
Outdoor Limited Ranger Joe's
Ranger Joe's Upstate Tactical Supply
Upstate Tactical Supply Vigilant Gear
Vigilant Gear ARES – Alamance County
ARES – Alamance County Center Mass Group
Center Mass Group CERT Training
CERT Training Greenside Training
Greenside Training Hogwarts School of Grid-Down Medicine
Hogwarts School of Grid-Down Medicine Land Nav 101
Land Nav 101 Mason Dixon Tactical
Mason Dixon Tactical Max Velocity Tactical
Max Velocity Tactical Randall's Adventure and Training
Randall's Adventure and Training Rockwell Tactical Group
Rockwell Tactical Group S. C. Gun School
S. C. Gun School S12 Defensive Training Group
S12 Defensive Training Group SF Medic
SF Medic Signal Corps
Signal Corps Sootch00 Channel on YouTube
Sootch00 Channel on YouTube Georgia Militia
Georgia Militia TRADOC G2 Land Navigation Course Basics
TRADOC G2 Land Navigation Course Basics
Feb 18, 2017 @ 09:26:07
I would like to participate. Where is the "park" location and how do I become part of the organization?
Thank you.
Stan
Sent: Wednesday, February 15, 2017 at 4:10 PM
Mar 01, 2017 @ 10:33:08
Stan, it pains me to say this, but right now we’re in the middle of a training cycle and can’t really take on anyone, regardless of qualifications, until about june. and equally painful is to recommend you search for a group in your area over at modern militia movement. our listing over there keeps disappearing, maybe because we’re not militant and outspoken enough for them. and just beware of any group that only exists on facebook. they’re doing it wrong.